{fastsocialshare}
Finally! State-of-the-art Medical Device IT Security Requirements! And they are free! And you can download them!
For those of us who (in vain) have poured over IT Security standards and guidelines of variable quality in order to distillate useful requirements: look no further! A state-of-the-art, useable Medical Device IT Security guideline is finally here!
The Johner Institute has in collaboration with TÜV SÜD, TÜV Nord and Dr. Heidenreich (Siemens) compiled an excellent set of Medical Device Cyber Security Process and Product requirements and made it available to the industry for free.
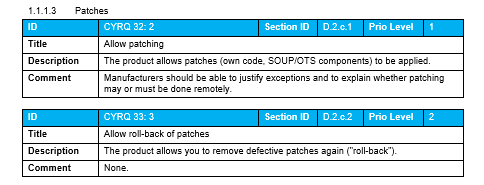
Roughly 150 IT Security requirements are available in the Guideline covering both process requirements as well as product requirements, including the level of expertise needed to implement them, are available in the following structure:
Process requirements
Requirements for the development process
- Intended purpose and stakeholder requirements
- System and software requirements
- System and software architecture
- Implementation and development of the software
- Evaluation of software units
- System and software tests
- Product release
Requirements for the post-development phase
- Production, distribution, installation
- Market surveillance
- Incident response plan
Product requirements
- Preliminary remarks and general requirements
- System requirements
- System and software architecture
- Support materials
This IT Security Guideline is directed to Medical Device Manufacturers as well as Auditors, Reviewers, and Hospital Management.
Dr. Johner and his collaborators have in this guideline managed to deliver concrete, best-practice guidelines, something that most other standards and regulations certainly tend to lacks.
The entire guideline is available in the GitHub-Repository „IT Security Guideline“ (https://github.com/johner-institut/it-security-guideline/) and is a recommended read for everyone concerned with Medical Device cybersecurity. You can also download Excel files with the requirements from the Johner Institute website.
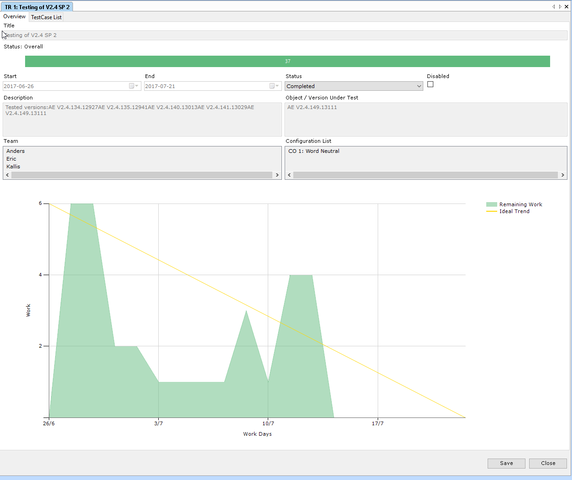
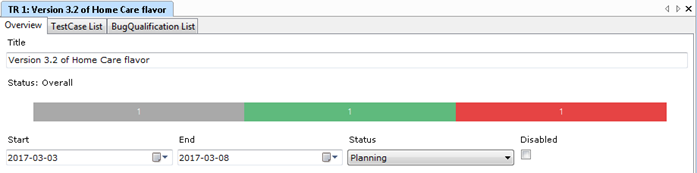
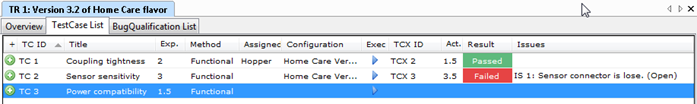
We have made the Product IT Security Requirements available as a downloadable extension for Aligned Elements. It is recommended to use them in conjunction with the material in the mentioned GitHub-repository, which contains valuable additional information and footnotes that explain the rationale and context for some of the requirements.


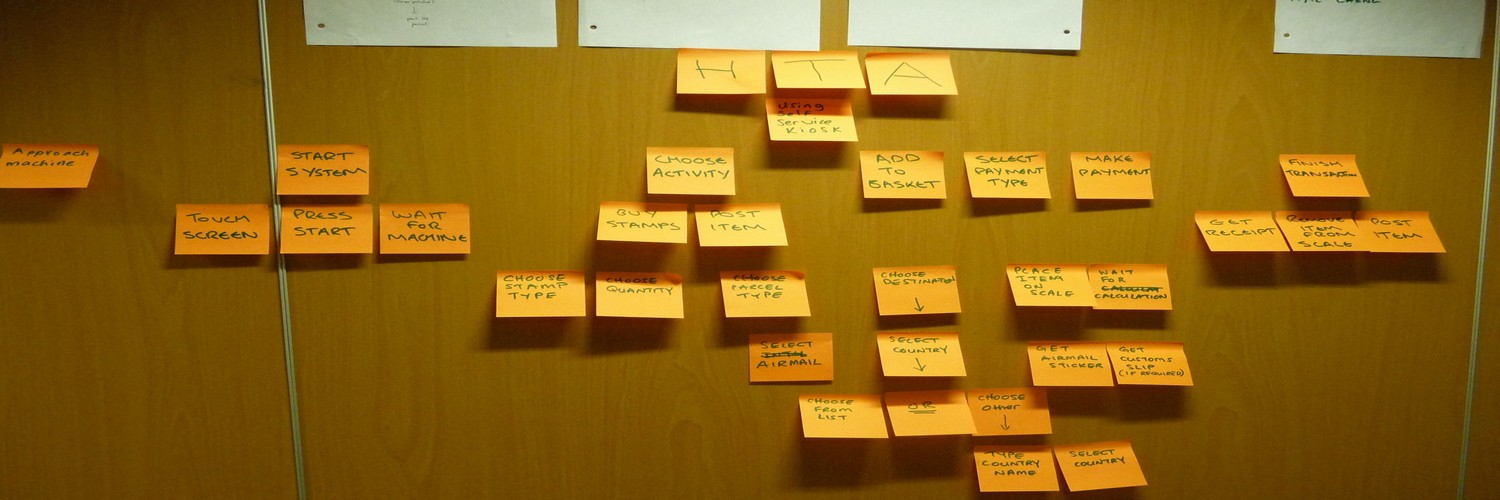
 It is rather rare that the developer has the real and deep experience a User has and it can therefore be precarious to leave the User Need elicitation process in the hands of an engineering team. Here are some tips for eliciting better User Needs.
It is rather rare that the developer has the real and deep experience a User has and it can therefore be precarious to leave the User Need elicitation process in the hands of an engineering team. Here are some tips for eliciting better User Needs.